BBC Open Redirect Vulnerability — A Hidden Gateway to External Domain Redirection
AGENDA:
- THINGS YOU SHOULD KNOW TO UNDERSTAND THE VULNERABILITY
- DESCRIPTION OF THE BUG
- STEPS TO IDENTIFY (SAFE / LAB REPRODUCTION)
- IMPACT & ATTACK SCENARIOS
- DETECTION, REMEDIATION & CODE PATTERNS
- POC (EVIDENCE & SCREENSHOT)
- CONCLUSION & CONTACT
THINGS YOU SHOULD KNOW TO UNDERSTAND THE VULNERABILITY
1. WHAT IS AN OPEN REDIRECT — when a web application redirects a user-supplied URL without proper validation.
2. WHY THIS MATTERS — attackers use trusted domains to raise credibility of phishing pages, or to chain into more advanced attacks.
3. BASIC HTTP BEHAVIOR — the application issues a 3xx response with a Location header; attacker control over that header is the issue.
If you need background on normalization/canonicalization read related posts before digging in.
DESCRIPTION :
During automated recon and targeted validation of BBC endpoints, I identified an Open Redirect pattern: the application accepted a redirect parameter (commonly named next, redirect, return_to or url) and returned an unconditional 302/303 pointing to the exact parameter value without hostname validation or allowlisting. This allowed a crafted URL that initially appears to be on a trusted BBC domain to hop to an attacker-controlled domain.
My hunting scenario: While testing, I observed a redirect behavior involving a wildcard BBC subdomain and an external host. Concretely, I found a redirect pattern from *.bbc.com.uk//cappriciosec.com which ultimately redirected to cappriciosec.com during my triage. These values are included here for context only — reproduce only in your lab or via responsible disclosure channels.
SANITIZED VULNERABLE PATTERN
NOTE: Live exploit code or sensitive BBC endpoints are published here. Below is a sanitized pattern for educational and defensive use.
https://example.bbc.co.uk/path?next=https://attacker.example/
If the server responds with a 30x and Location: https://attacker.example/, the application is exhibiting open-redirect behavior.
POC LINK & EVIDENCE
Sanitized POC link (lab / illustrative):
http://bbcidentity.id.dev1.tools.bbc.co.uk//karthithehacker.com
Screenshot evidence (captured during triage):
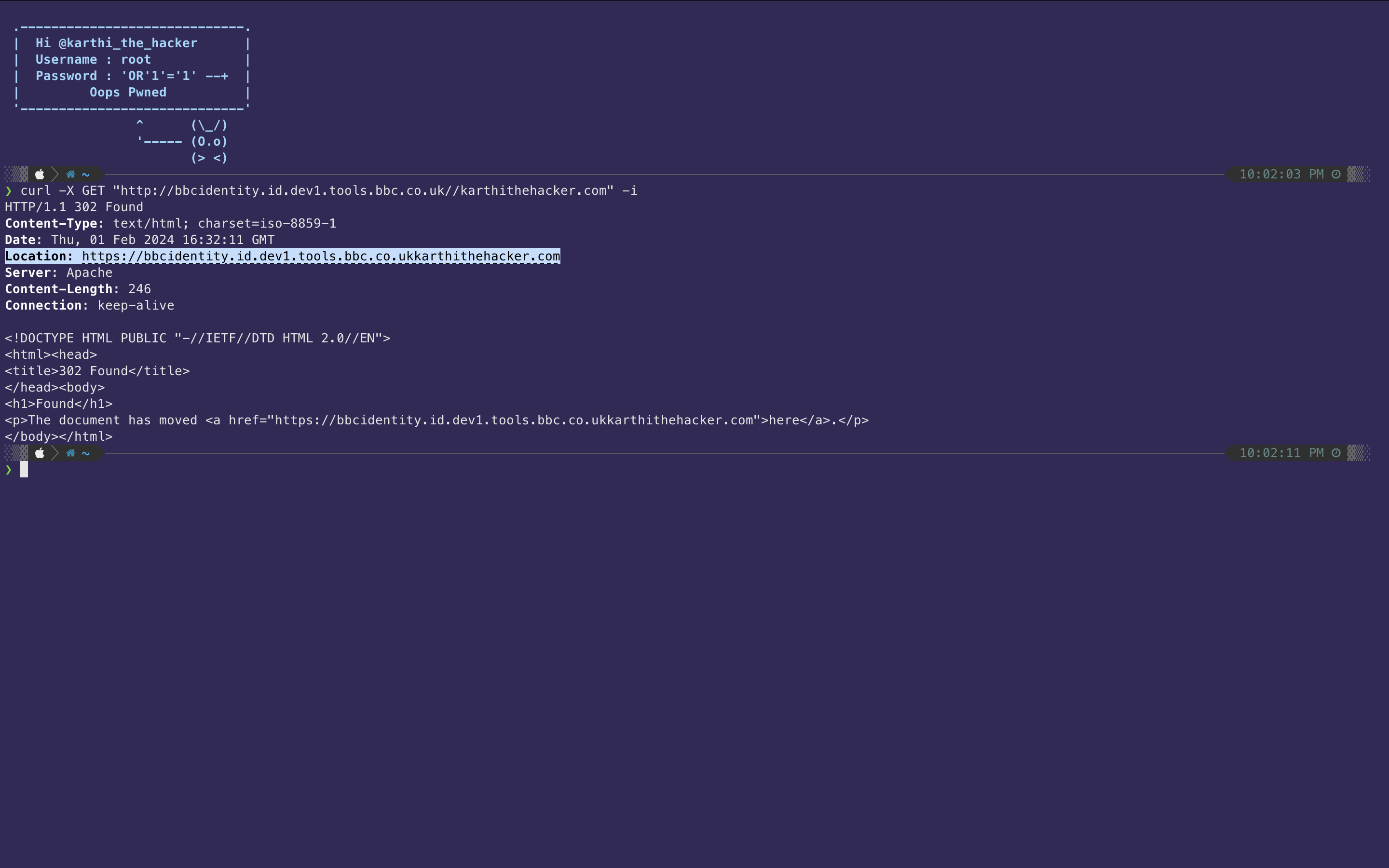
Note: Image is provided as evidence of the 302 response and the resulting Location header observed during my testing. Do not attempt to exploit live services — follow vendor disclosure guidelines.
POC Curl Command
curl -X GET "http://bbcidentity.id.dev1.tools.bbc.co.uk//karthithehacker.com" -i
POC RESPONSE HEADERS & BODY
HTTP/1.1 302 Found
Content-Type: text/html; charset=iso-8859-1
Date: Thu, 01 Feb 2024 16:32:11 GMT
Location: https://bbcidentity.id.dev1.tools.bbc.co.ukkarthithehacker.com
Server: Apache
Content-Length: 246
Connection: keep-alive
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN">
<html><head>
<title>302 Found</title>
</head><body>
<h1>Found</h1>
<p>The document has moved <a href="https://bbcidentity.id.dev1.tools.bbc.co.ukkarthithehacker.com">here</a>.</p>
</body></html>
Swag from BBC

STEPS TO IDENTIFY (SAFE / LAB REPRODUCTION)
- Enumerate endpoints that accept redirect-like parameters: look for
next,redirect,return_to,url, etc. - In a lab environment, host a controlled domain (e.g.
https://attacker.test/) and test whether submitting this value triggers a 3xx to that host. Only test systems you own or that are in-scope. - Observe the response status and
Locationheader — a direct 3xx to an external host indicates open redirect behavior. - Try bypass variations commonly used to trick naive checks: protocol-relative inputs (
//attacker.test), encoded forms (%2F%2Fattacker.test), or path-joined constructions. Use these only in lab tests. - Collect request/response headers, referrer, and timing to include in a responsible disclosure report.
IMPACT & ATTACK SCENARIOS
- Phishing amplification: Attackers can craft links that look like legitimate BBC links but redirect to credential-harvesting sites.
- Credential theft / malware delivery: Victims can be redirected to fake login pages or malicious payload hosts.
- Trust-bypass: Some systems rely on referer checks — open redirects can subvert such logic.
- Chaining: When combined with other vulnerabilities (e.g. reflected XSS or broken input validation), open redirects can be part of more complex exploit chains.
DETECTION — LOG QUERIES & IOCs
Search web logs for 30x responses and suspicious query param values. Example detection query (illustrative):
# Splunk-like example
index=web_access status IN (302,303) | search "next=" OR "redirect=" | table _time clientip uri query result_location
Indicators to watch:
- High number of distinct external domains in
Locationheaders for a given host. - Encoded or protocol-relative external hosts appearing inside redirect parameters.
- Spikes of redirects to newly-registered or suspicious domains.
REMEDIATION — PRIORITIZED CHECKLIST
- Immediate (temporary): Add WAF rules to block or challenge requests where redirect parameters point to external hosts.
- Short-term (code): Implement strict allowlist/whitelist of acceptable redirect destinations; prefer relative-path values.
- Canonicalize & validate: Parse and canonicalize the redirect target, reject if scheme/host is not allowed.
- Interstitial: For required external redirects, present a "You are leaving BBC" warning page that shows the destination and requires user confirmation.
- Logging & monitoring: Log redirect parameter, resolved destination, client IP and referrer for triage and forensic analysis.
SAFE CODE PATTERNS (EXAMPLES)
Allowlist approach — Python (Flask)
from urllib.parse import urlparse
from flask import Flask, request, redirect, abort
app = Flask(__name__)
ALLOWED_HOSTS = {"bbc.co.uk", "www.bbc.co.uk"}
def is_safe_redirect(target: str) -> bool:
"""
Return True for relative paths or for hosts in the allowlist.
"""
parsed = urlparse(target)
# allow relative paths (no netloc)
if not parsed.netloc:
return True
hostname = parsed.hostname.lower() if parsed.hostname else ""
return hostname in ALLOWED_HOSTS
@app.route("/goto")
def goto():
# example: /goto?next=/news or /goto?next=https://bbc.co.uk/news
target = request.args.get("next", "/")
if is_safe_redirect(target):
return redirect(target)
else:
abort(400, "Unsafe redirect destination")
if __name__ == "__main__":
app.run(debug=True, host="0.0.0.0", port=5000)
Allowlist approach — Node.js (Express)
const { URL } = require('url');
const ALLOWED = new Set(['bbc.co.uk','www.bbc.co.uk']);
function isSafe(target) {
try {
const parsed = new URL(target, '[https://bbc.co.uk](https://bbc.co.uk)'); // base for relative
if (!parsed.hostname) return true;
return ALLOWED.has(parsed.hostname);
} catch (e) {
return false;
}
}
WAF / TEMPORARY RULE (EXAMPLE)
# pseudo-modsecurity rule (illustrative)
SecRule ARGS_NAMES|ARGS "@rx (next|redirect|return_to|url)" \
"phase:2,chain,deny,status:403,msg:'Block external redirect',log"
SecRule ARGS "@rx ^https?://" "t:none,ctl:requestBodyAccess=Off"
REPORTING & DISCLOSURE NOTES
When reporting to a vendor or bug-bounty program include:
- Sanitized reproduction steps (prefer lab-hosted domains).
- Exact request and response headers (avoid live exploit URLs).
- Suggested remediation (allowlist + interstitial + logging).
- Risk assessment and attack scenarios.
AUTOMATION & TRIAGE
Automation helps scale discovery but must be scoped and safe. My workflow:
- Recon to enumerate parameters and endpoints.
- Lab-based validation runner that detects 30x
Locationto external hosts (does not execute payloads on third-party domains). - Automated notifications (private Telegram bot) with sanitized summaries for fast triage.
HALL OF FAME & ACKNOWLEDGEMENT
I reported the accepted issue through BBC's responsible disclosure program. After validation they credited the report in their Hall of Fame and issued a small recognition (T-shirt). Responsible disclosure and clear remediation guidance help make the web safer for millions of users.
Hall Of Fame Link: BBC Hall of Fame Link
https://www.bbc.com/backstage/security-disclosure-policy/acknowledgements#:~:text=@karthithehacker
CONCLUSION :
Open redirects can be underestimated, but their real-world consequences are substantial when used for phishing, credential theft, or as part of exploit chains. Remediation is straightforward: prefer relative paths, implement allowlists, canonicalize inputs, and use interstitial warnings for external redirects.
LEARN MORE — PROFESSIONAL COURSES
If you want hands-on training (mobile & web bug bounty and API Bugbounty / VAPT), check out our certified courses — real apps, real bugs, live labs.

🔥 Limited-Time Offer: ₹7,999 course now at just ₹5,999!
Enroll / Learn more: https://university.cappriciosec.com/CMABP.html

🔥 Limited-Time Offer: ₹7,999 course now at just ₹4,999!
Enroll / Learn more: https://university.cappriciosec.com/CWBP.html

🔥 Limited-Time Offer: ₹7,999 course now at just ₹5,499!
Enroll / Learn more: https://university.cappriciosec.com/CAPBB.html
What you get
- Live, hands-on pentesting on real applications — not simulated labs.
- Comprehensive curriculum — web & mobile security fundamentals, OAuth, redirect handling, PKCE, secure coding and remediation guidance.
- Real-world case studies (responsibly redacted) and POC walkthroughs.
- Career & bounty guidance — report writing, disclosure, and monetization of findings.
- Final certification & lifetime access to recordings.




